Mobile device
Mobile deviceInformation
English (United States)
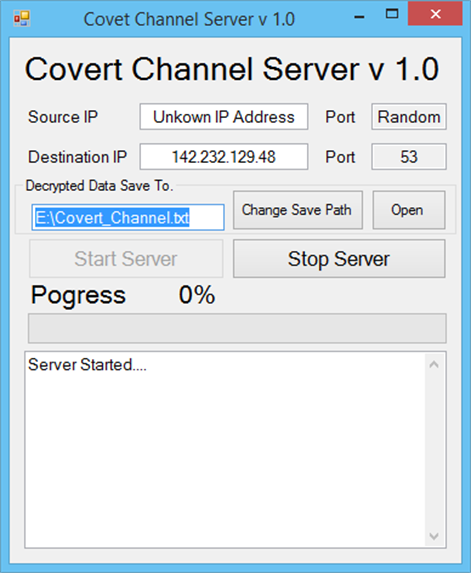
Description
I made this as a my final project of CST Btech program at BCIT.
Encrypted Covert channel is a type of computer software attacks that allow the communication of information by transferring objects through existing information channels or networks. It uses the structure of the existing medium to convey the data in small parts. This makes conveyance through a covert channel virtually undetectable by administrators or users. Covert channels have been used to steal data from highly secure systems.
Encrypted Covert channel can pass the undetected payload through most firewalls and IDS (Intrusion Detection System) hiding its data in a packet header or payload. It camouflages its data as a part of an ordinary packet header or a packet body so that packets pass most firewalls and IDSs. However, covert channel also can be detected by an intelligent IDS or highly skilled network administrators even though it can hide the data in Sequence number or ACK (Acknowledge) of TCP/IP header reserved field or use a tool. The encrypted covert channel can prevent extracting the encrypted payload in any case. This technique can be applied to TCP and UDP packets both. This project adopts the UDP covert channel to implement. Covert channel is created by using some of the space available either within the padding or within other parts of the transport of network packets. Covert channels use any means where data can be added to a data stream without affecting the main body of data being transmitted. This allows the covert receiver to abstract data from a system without creating any type of data trail. A single packet might only contain one or two bytes of the covert data stream, making a detection very difficult. Creating a covert channel takes some ingenious programming, and access to the file system at the source end of the communication is essential. This means that a covert channel can only be instigated through viral infection or through a programming effort that has administrative or other authorized access to the system.
People also like
Reviews
-
2/21/2018by Patrick
Very basic app. Doesn't hide your internet IP
-
8/15/2015by James
Good